A Methodology,
Not a Checklist.
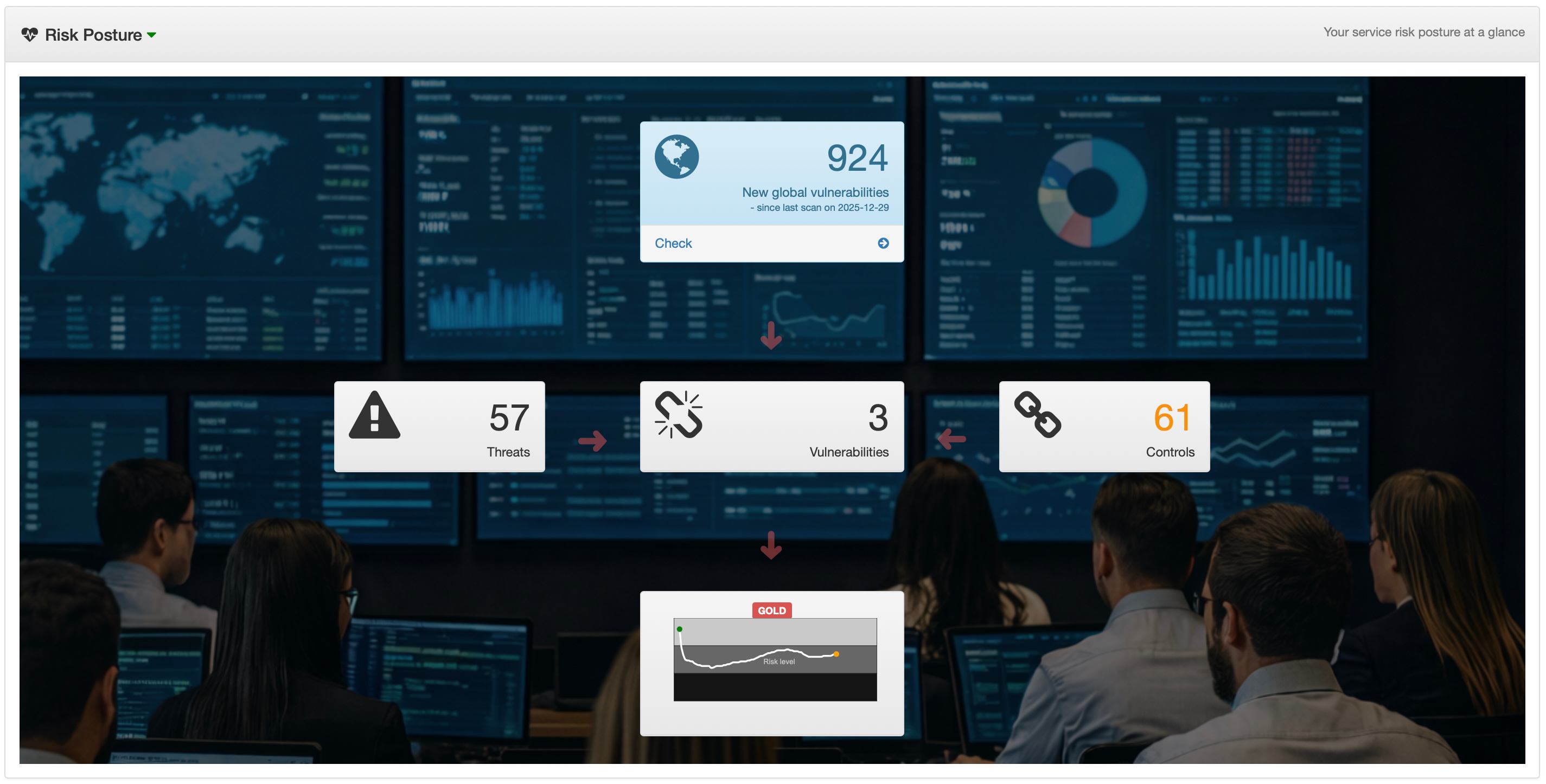
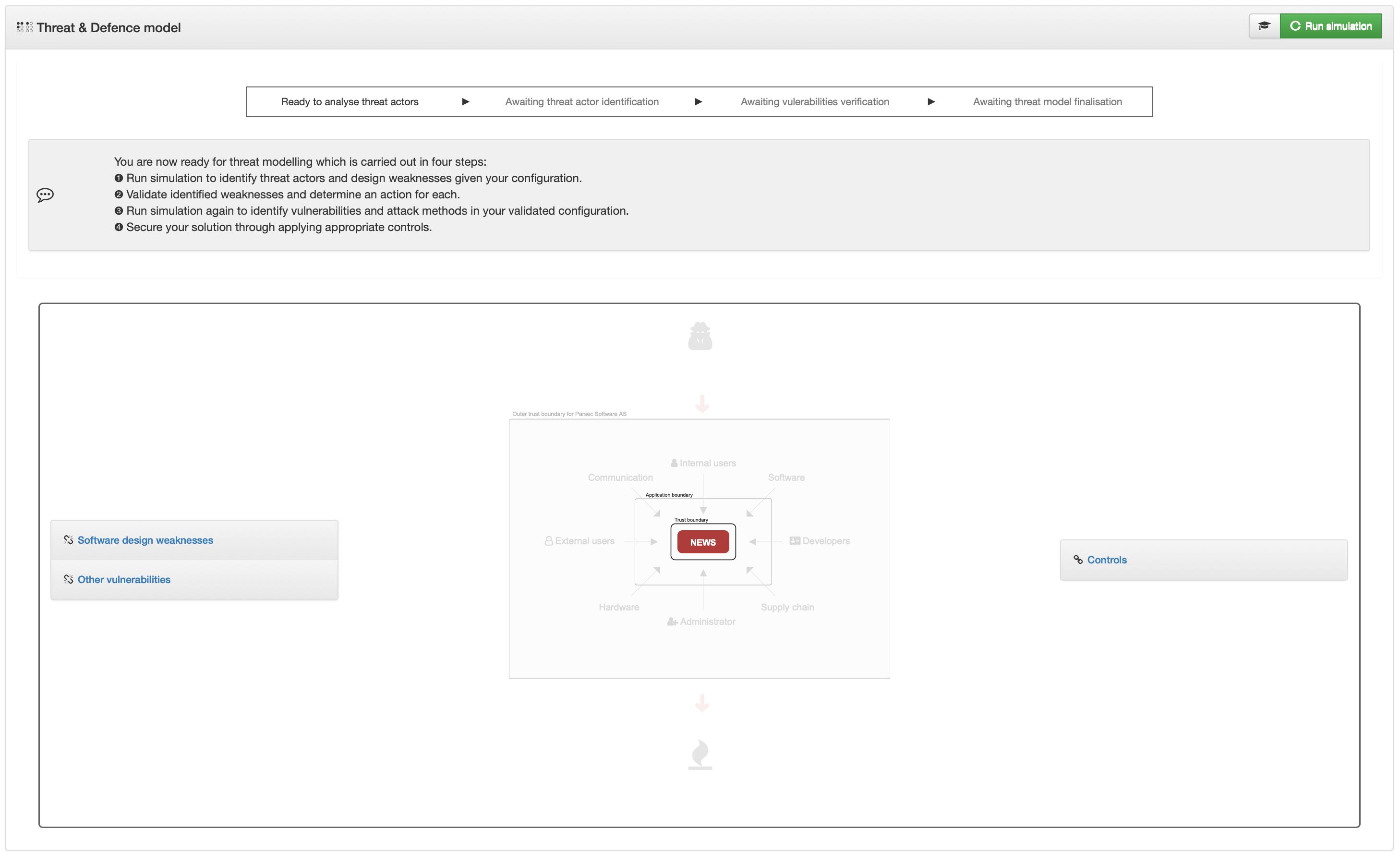
Four phases. Continuous, actionable results. The more precise your stack input, the more targeted the analysis.
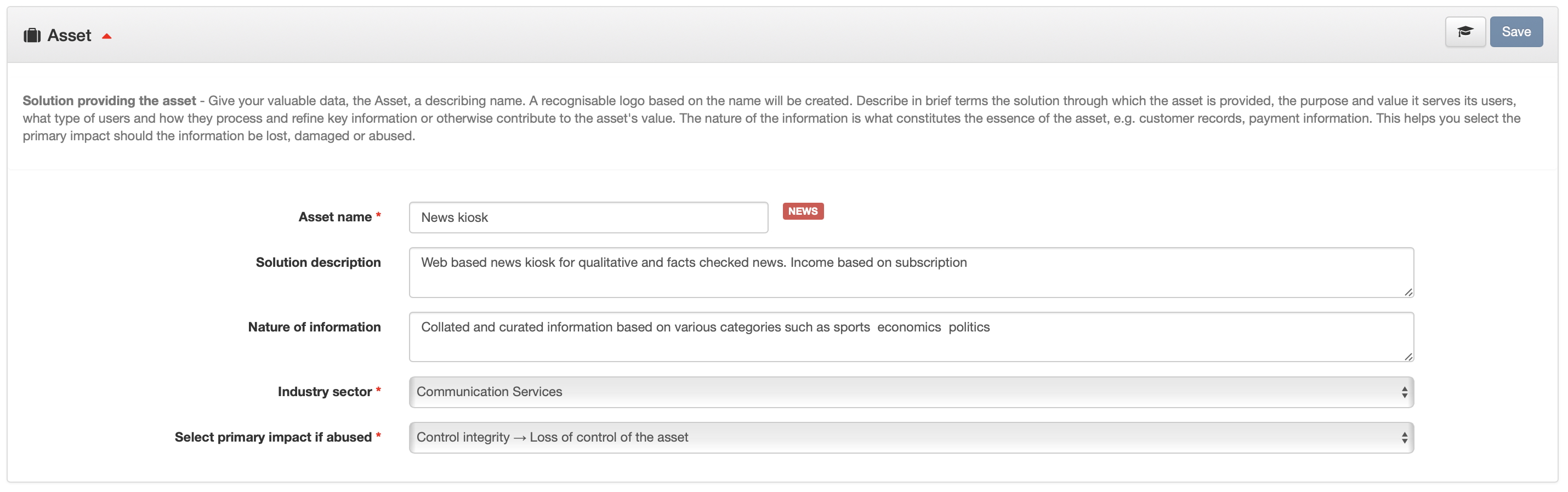
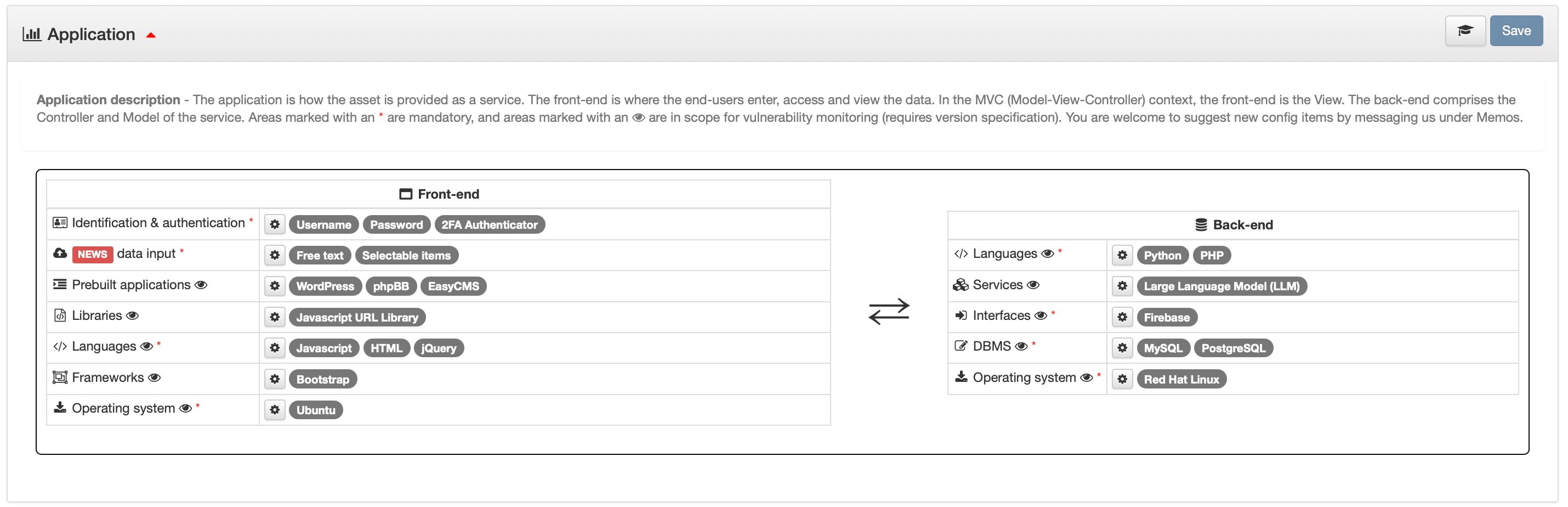
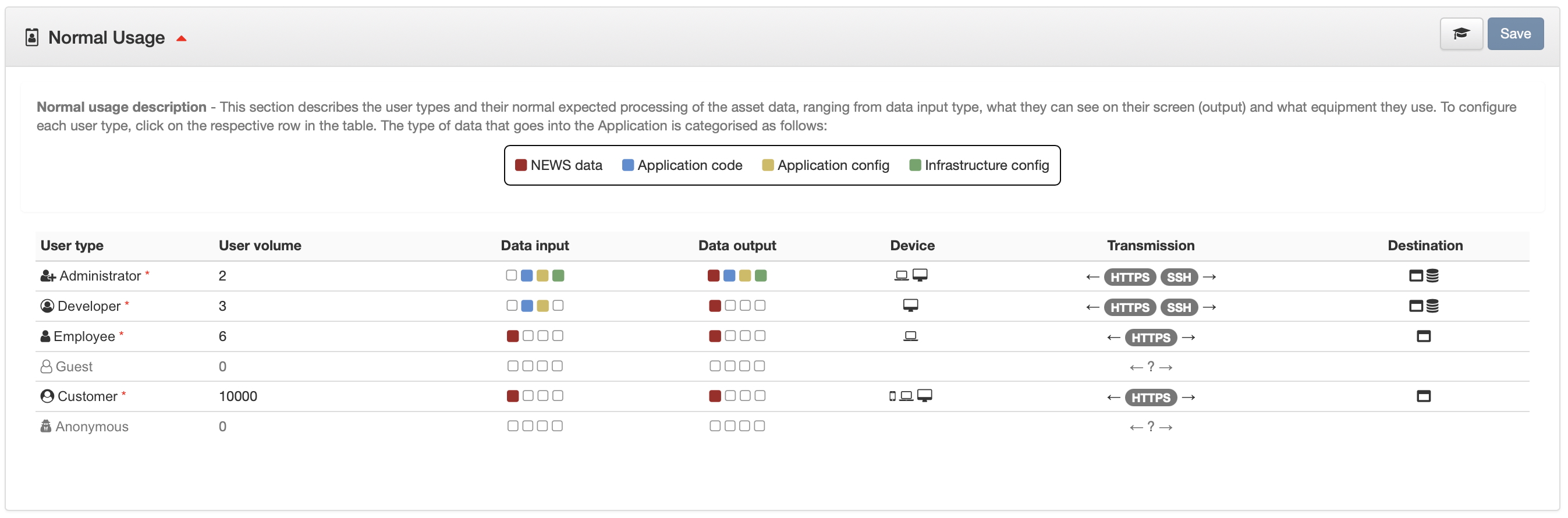
Register your asset, front-end framework, back-end services, libraries, protocols and user types. Precision input drives precision output.
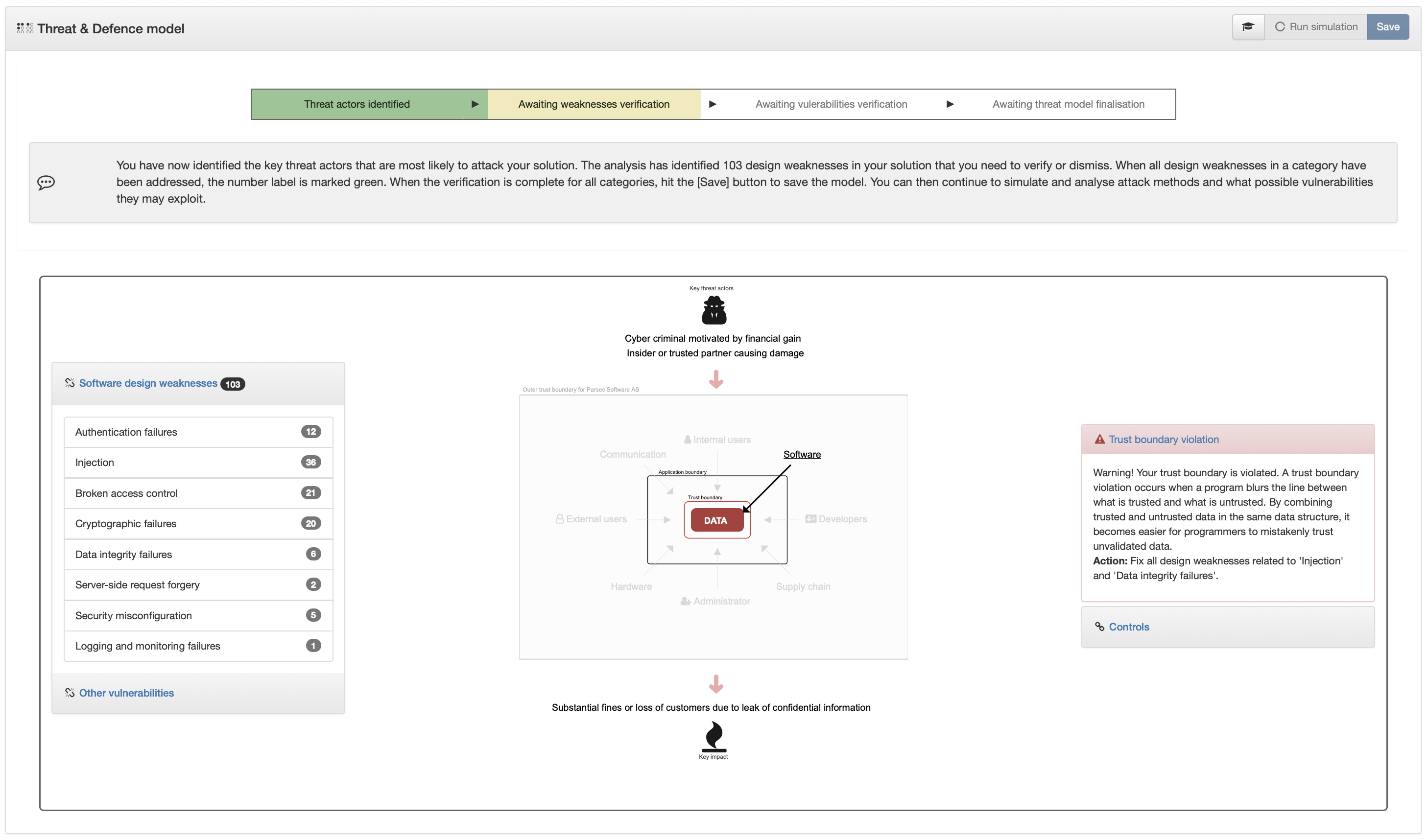
Cross-reference your configuration against the Common Weakness Enumeration to surface design-level weaknesses before code ships.
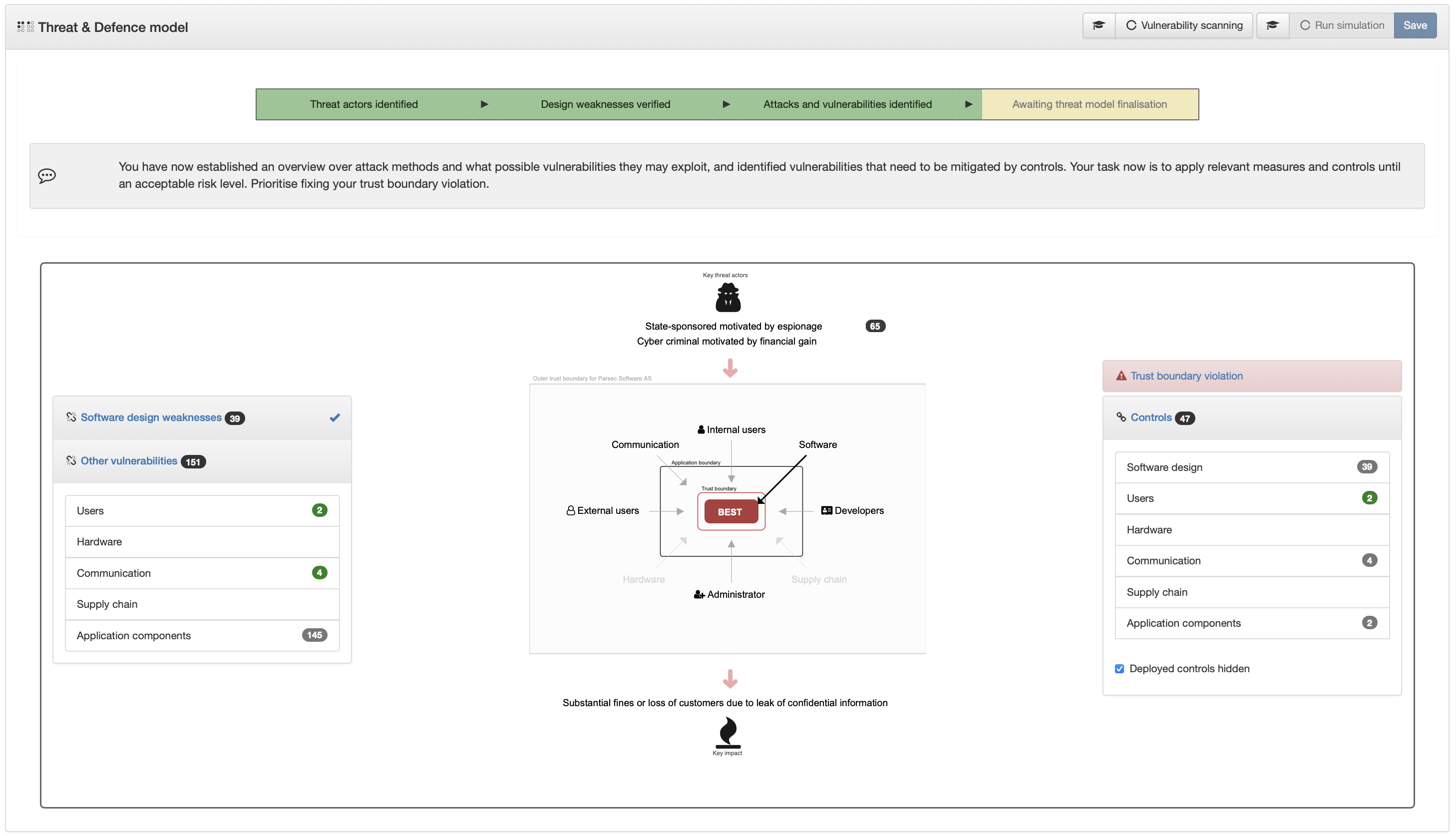
Simulate adversaries via CAPEC patterns—revealing attack methods, lateral paths, and supply chain exposure specific to your stack.
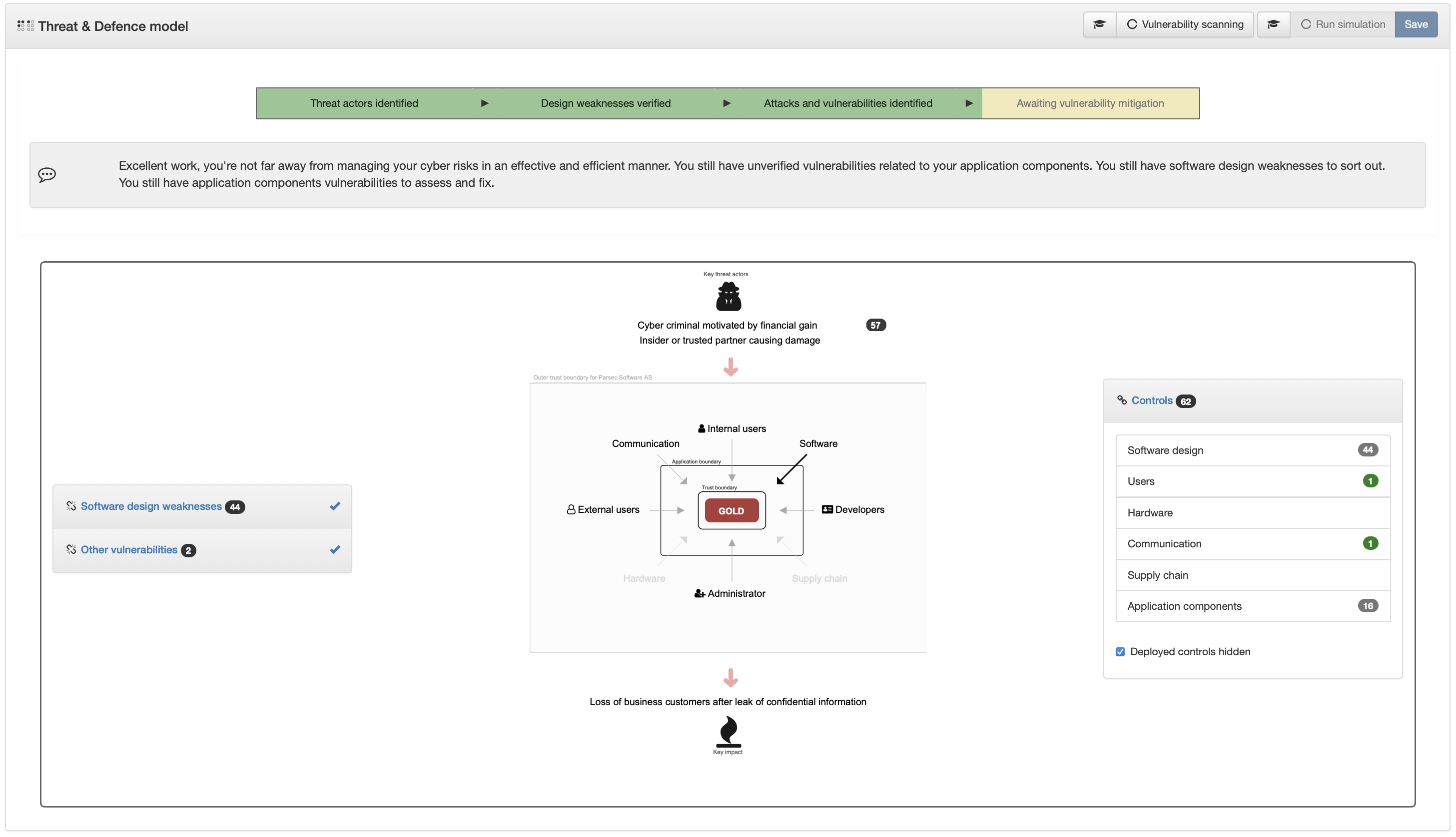
Register components with version numbers. Daily delta checks against the CVE database flag new vulnerabilities scoped only to what you actually run.