Customer Trust
Starts With
Cyber Trust
Earning customer trust takes time. Losing it takes only one vulnerability. Manage your risks. Protect your reputation.

Earning customer trust takes time. Losing it takes only one vulnerability. Manage your risks. Protect your reputation.


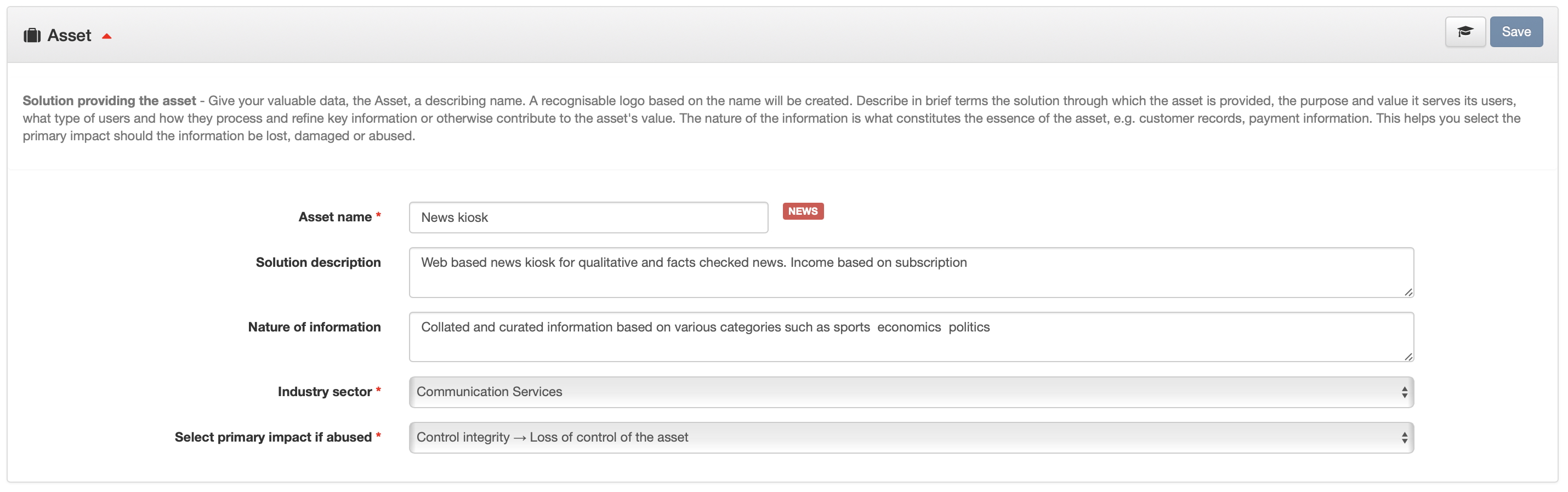
A structured threat modelling workflow grounded in MITRE and OWASP standards — not a generic scanner.
This has offloaded tedious but important work that otherwise would have been neglected. We also discovered a design miss that had totally gone under the radar.
The design of our online service was verified ok, which is good, but the vulnerability monitoring is what truly adds value. Love the riskogram!
By leveraging your service, we've learnt to proactively defend our online assets, maintain customer trust, and stay ahead of emerging cyber threats at a very reasonable cost.
Three steps to cyber clarity. Register, verify, and start protecting your business today.
Manage your risks. Protect your reputation. Discover weaknesses before they are exploited. Simulate real-world attacks and stay secure every day — either through our intuitive platform or via our fully managed service.
What's your approach? Don't just react to disruptions. Prioritize long-term resilience and system reliability to keep your customers' data safe.
Resilience over reaction.
"Treating cybersecurity as a go-to-market advantage is the key to winning customer trust in the age of AI."
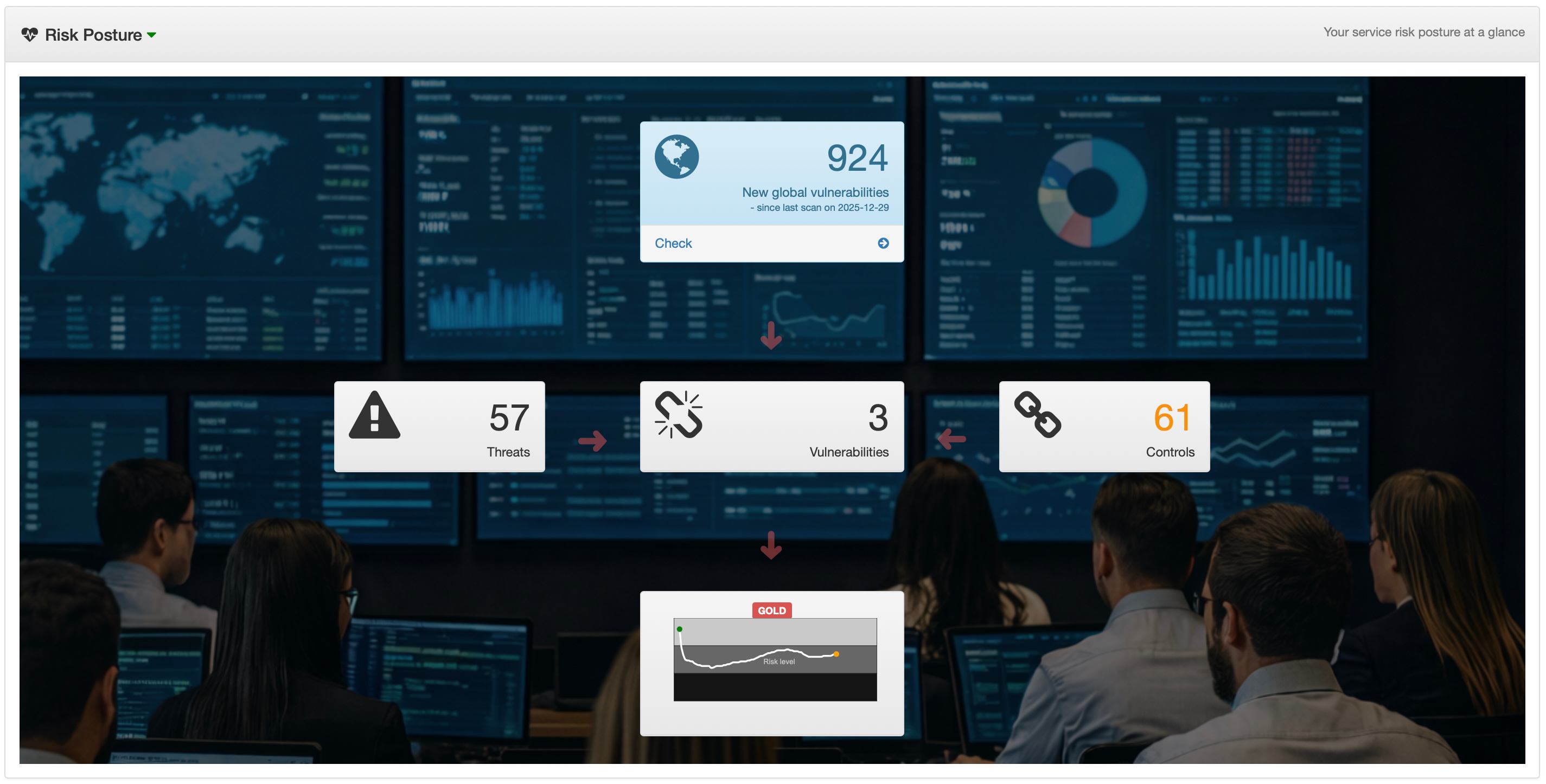
cyberriskguru is designed to unlock supporting features as you grow. Above shows the Risk Posture which unlocks at 50% maturity.
Visit our YouTube channel for our educational videos
If you're at an apprentice level, you'll find great resources that will bring you up to speed on various cyber security and risk topics.
Understand important cyber risk topics in depth through educational videos.
Extensive tutorials that help you with threat modelling, risk assessments and cyber strategy planning and execution.
Hit the subscribe button in our channel to make sure you're informed about new videos.